Dec 31st 2013, 16:50, by Matthew Panzarino
Apple has contacted TechCrunch with a statement about the DROPOUTJEEP NSA program that detailed a system by which the organization claimed it could snoop on iPhone users. Apple says that it has never worked with the NSA to create any ‘backdoors’ that would allow that kind of monitoring, and that it was unaware of any programs to do so.
Here is the full statement from Apple:
Apple has never worked with the NSA to create a backdoor in any of our products, including iPhone. Additionally, we have been unaware of this alleged NSA program targeting our products. We care deeply about our customers’ privacy and security. Our team is continuously working to make our products even more secure, and we make it easy for customers to keep their software up to date with the latest advancements. Whenever we hear about attempts to undermine Apple’s industry-leading security, we thoroughly investigate and take appropriate steps to protect our customers. We will continue to use our resources to stay ahead of malicious hackers and defend our customers from security attacks, regardless of who’s behind them.The statement is a response to a report in Der Spiegel yesterday that detailed a Tailored Access Operations (TAO) unit within the NSA that is tasked with gaining access to foreign computer systems in order to retrieve data to protect national security. The report also pointed out a division called ANT that was set up to compile information about hacking consumer electronics, networking systems and more.
The story detailed dozens of devices and methods, including prices for deployment, in a catalogue that could be used by the NSA to pick and choose the tools it needed for snooping. The 50-page catalog included a variety of hacking tools that targeted laptops and mobile phones and other consumer devices. Der Spiegel said that these programs were evidence that the NSA had ‘backdoors’ into computing devices that many consumers use.
Among these options was a program called DROPOUTJEEP — a program by which the NSA could theoretically snoop on ‘any’ Apple iPhone with ’100% success’. The documents were dated 2008, implying that these methods were for older devices — and there was no reference on any of them to iOS versions newer than iOS 5. Still, the program’s detail was worrisome.
Researcher and hacker Jacob Applebaum — the co-author of the articles, coinciding with a speech he gave at a conference about the programs — pointed out that the ’100% success rate’ claimed by the NSA was worrisome as it implied cooperation by Apple. The statement from the company appears to preclude that cooperation.
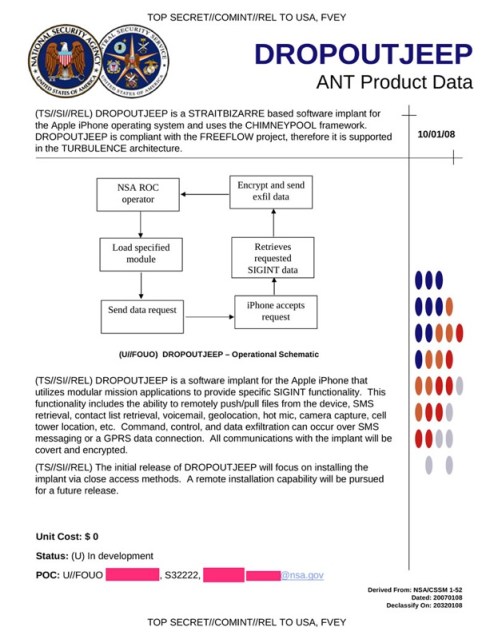
The program detail indicated that the NSA needed physical access to the devices at the time that the documents were published. It does note that they were working on ‘remote installation capability’ but there’s no indication whether that was actually successful. The program’s other options included physical interdiction of devices like laptops to install snooping devices, but there have been security advances like hardware encryption in recent iPhone models that make such installation of devices much more difficult.
More to follow…

No comments:
Post a Comment